Image links now being used in USPS email malware scam
July 10, 2012
UPS, USPS and other courier name email scams are nothing new. We've seen UPS, DHL and FedEx spoofed for several years in various malware campaigns. The payloads are usually delivered via malware laden attachments, disguised as invoices, shipping labels, or pickup instructions, which the victim is supposed to open and print out. This week there is a new twist to the courier scams: clickable images containing a message and instructions to click to "print a shipping label."
The scams I have intercepted over the last two weeks or so spoof two services in the same message: UPS (United Parcel Service) and USPS (United States Postal Service). Either the spammers who write the text for these scams aren't aware that these are two different entities, or are counting on recipients overlooking this fact and falling for the bait due to recognizing the names.
In either case, the purpose of these messages, like those before them, is to infect unwary email recipients with Trojans, like the ZeuS bank account stealing malware, a botnet installer, a backdoor remote controller, and sometimes, fake security programs that demand money to fix non-existent problems (the pop-up desktop alerts are fake and themselves are the problem!), or fake FBI or other Police notices which hold the computer hostage until a ransom is paid for alleged bad behavior.
The courier scams are sent in bulk to everybody (via botnetted PCs), but are really targeting businesses and people who frequently send or receive goods via UPS or USPS, like eBay buyers and sellers. The criminals responsible (in Russia) are hoping that a busy secretary or shipper will open the attachment, or click on the link without thinking it through, or reading all of the text carefully (for giveaway typos or mixed up brand names).
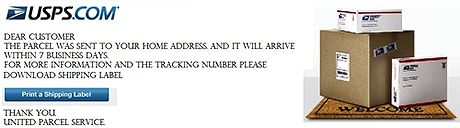
Next, let's take a look at the image being used in the latest incarnation of the UPS/USPS email scams.
In order to get past spam filters, spammers frequently change the templates they use to compose their messages. They have gone to great effort to hide these current USPS image scams from detection, by adding hidden text that is styled to be white, against the standard white background of the email message window. The text, although plainly readable if highlighted by one's pointer, is an excerpt from the book titled: War-Time Silhouettes, but looks like possibly normal correspondence to an anti-spam program.
Why, you ask, do they do this? To confuse spam filtering programs looking for image spam.
Around 2008, in an effort to get past spam filters looking for certain keywords, spammers began blasting out email messages with nothing but images containing embedded text, promoting counterfeit drugs and pump and dump stocks. Most didn't even provide a clickable link, but embedded a website address in the spam text in the image, which the gullible were suppose to type into their browser's address bar. This embedding of text into an image is done using a graphics editor, like Adobe Photoshop.
As a result, spam filtering programs were retrained to look for just an image sent with or without a link, then flag them with the word "{SPAM} or {POSSIBLE SPAM} in the subject. The recipients are then alerted and will be wary of anything contained in those messages.
By using "Salad Words" or excerpts from publications, along with images containing an embedded textual message, spammers have a better chance of getting their emails past spam filters, to be viewed by many potential victims.
So, what does the image look like in the current USPS/UPS email spam campaign? Behold!
Notice how, despite most of the wording and photos are for the United States Postal Service (USPS.com), the bottom left says "Thank You" "United Parcel Service?" A mixup by offshore writers, or deliberate subterfuge? Also, it is impossible to miss the button labeled: "Print a Shipping Label." In fact, you don't need to click on that (fake) button, because the entire image is wrapped inside a clickable link. Anybody clicking on the link in the spam message is taken to a website controlled by these spammers and presented with the following JavaScript function: window.location="USPSLabel.zip"
That code causes a Save or Run box to pop-up, with "USPSLabel.zip" as the file name. If the zip file is opened the malware code will be unleashed. If it cannot autorun, due to your computer's OS or security settings, you will be presented with a prompt to click to display the contents. This causes the Trojan installer to run. If you are a Limited or Standard User, you will be shown a UAC prompt in Windows Vista or 7. If you proceed, your computer will be pwned by a botmaster, the ZeuS banking Trojan will be installed and bad things will happen to your financial accounts, other malware will be downloaded to your PC, your computer will send out spam and may be used in DDoS attacks on innocent websites or Governments.
Spam reporters and alert email recipients will recognize the text message that has been embedded in the scam image, from previous scams for USPS and UPS (Which begins with a copy of actual US Post Office logo and USPS.COM and stack of boxes on right, with US Post Office tags and labels).
DEAR CUSTOMER;
THE PARCEL WAS SENT TO YOUR HOME ADDRESS AND IT WILL ARRIVE WITHIN 7 BUSINESS DAYS.
FOR MORE INFORMATION AND THE TRACKING NUMBER
PLEASE DOWNLOAD SHIPPING LABEL(Fake button labeled: "Print a Shipping Label")
THANK YOU
UNITED PARCEL SERVICE
I hope this heads-up keeps my busy friends and readers from accidentally clicking on this malware scam. The ZeuS and the botnet installer that comes with it are hard to irradicate. You'll need top-notch anti-malware program to remove these bad boys. If you get infected with this Trojan package and you are running an anti virus program, it failed you. Please check out a free trial of one of the Trend Micro Internet Security programs, which I use and recommend.
Keep in mind that malware purveyors pay people to frequently alter their codes and repack malware delivery packages to elude anti-virus definitions for a day or two. That's all the time they need to infect hundreds of thousands of unsuspecting Netizens. You not only need a modern anti-virus and anti-malware program , or programs, but a good dose of suspicion, user account protection (less than administrator privileges and UAC enabled) and common sense! A lot of these courier scams depend upon people lacking one or more of these attributes, as well as them not being fully up to date with their security program or its definitions.
Spammers send out millions of messages, via botnets, in the Chance that enough people will be gullible enough to fall for their carefully engineered come-ons. To avoid becoming one of their victims, remember that Chance favors the prepared mind. Learn to spot the tricks used by spammers and Chance will favor you.
If you like this article please share it.
 This weblog is licensed under a Creative Commons License.
This weblog is licensed under a Creative Commons License.The content on this blog may be reprinted provided you do not modify the content and that you give credit to Wizcrafts and provide a link back to the blog home page, or individual blog articles you wish to reprint. Commercial use, or derivative work requires written permission from the author.